Preparing for Employee Turnover: A Secure Data Destruction Plan for Departing Staff Devices
Safeguarding Sensitive Information During Transitions in Your Workforce
Employee turnover is a normal part of running a business. People move on to new roles, retire, or shift careers. While these transitions are routine, they can also create hidden risks, especially when it comes to company data stored on employee devices.
Laptops, desktops, and external drives often contain sensitive business information. If these devices are not handled properly when an employee leaves, data can be exposed, misplaced, or even misused. That is why having a clear and secure data destruction plan in place is not just helpful, it is essential.
For companies of all sizes, planning ahead can make the difference between a smooth transition and a costly data breach.
Why Employee Turnover Poses Data Risks
When employees leave, they often take with them access to systems, files, and tools they used daily. Even if access credentials are revoked quickly, the physical devices they used may still hold valuable information.
Common types of data found on employee devices include:
- Client and customer records
- Internal communications and emails
- Financial documents and reports
- Login credentials and saved passwords
- Proprietary business data
According to industry research, a significant percentage of data breaches are linked to internal sources, including former employees. This highlights the importance of taking data protection seriously during offboarding.
Without a structured approach, devices may be stored improperly, reused without proper handling, or discarded in ways that leave data vulnerable.
The Role of a Data Destruction Plan
A data destruction plan ensures that all company-owned devices are handled securely once they are no longer in use. It creates a repeatable process that reduces human error and protects sensitive information.
A strong plan focuses on:
- Accountability for every device
- Clear steps for collection and handling
- Secure methods of destroying stored data
- Proper documentation for compliance
For businesses that handle confidential or regulated information, having a documented process is often required to meet industry standards and legal obligations.
Building a Secure Offboarding Process
Creating a reliable plan starts with integrating data protection into your employee offboarding process. This ensures that security steps are not overlooked during busy transitions.
Device Inventory and Tracking
The first step is knowing exactly what devices an employee has used.
Maintain an updated inventory that includes:
- Laptops and desktops
- External hard drives
- USB storage devices
- Company-issued mobile devices
Before an employee leaves, confirm that all assigned equipment is returned. This simple step prevents devices from going missing and ensures nothing slips through the cracks.
Immediate Access Control
While physical devices are important, digital access should also be addressed at the same time.
Ensure that:
- Login credentials are disabled promptly
- Access to cloud systems is revoked
- Shared passwords are updated if needed
This reduces the chance of unauthorized access after departure.
Secure Collection and Storage
Once devices are returned, they should be stored securely until they are processed.
Best practices include:
- Keeping devices in a locked, access-controlled area
- Labeling items clearly to avoid mix-ups
- Limiting handling to authorized personnel
Even short-term storage should follow strict security measures, as data remains vulnerable until it is properly destroyed.
Choosing the Right Data Destruction Method
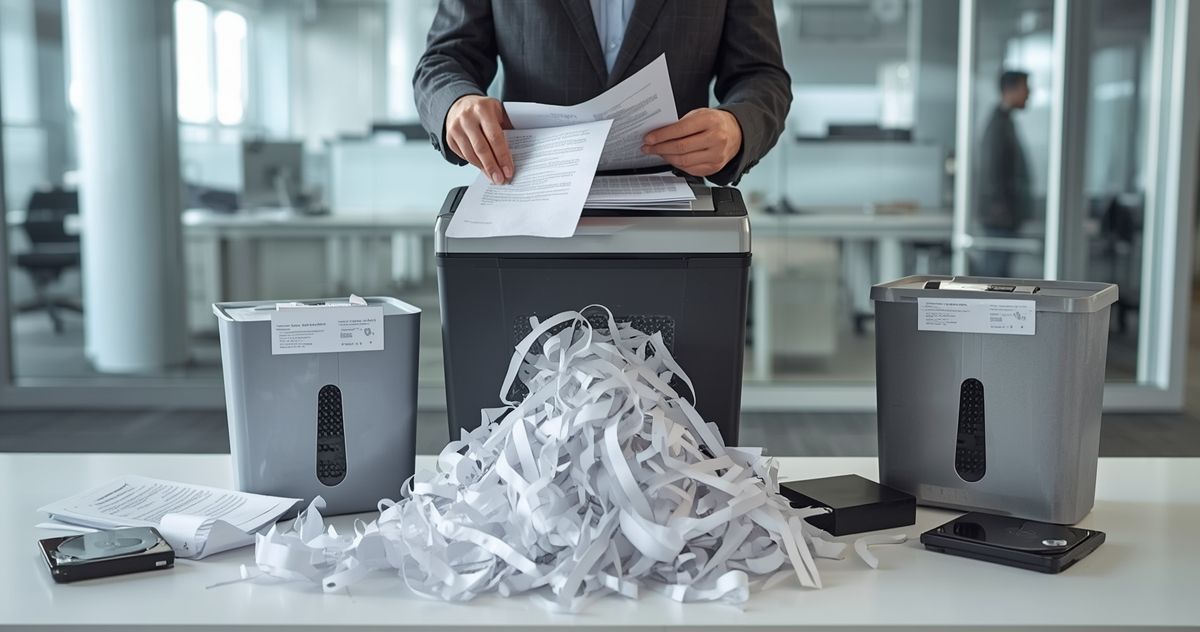
When it comes to protecting sensitive information, not all methods are equal. Simply deleting files or reformatting a device does not remove data completely. In many cases, information can still be recovered using specialized tools.
This is why businesses turn to professional solutions such as data destruction services to ensure complete and permanent removal.
Physical Destruction for Maximum Security
Physical destruction is one of the most reliable ways to eliminate data. This process involves breaking down storage devices so they can no longer be used or accessed.
Common approaches include:
- Crushing or shredding hard drives
- Destroying internal components of storage media
- Rendering devices unusable beyond repair
Services like hard drive shredding provide a high level of assurance that data cannot be recovered.
Certified and Documented Processes
For compliance and peace of mind, it is important to work with providers that offer verified procedures.
Look for services that provide:
- Certificates of destruction
- Detailed tracking of devices
- Secure handling throughout the process
Using certified hard drive destruction helps demonstrate that your business follows proper data protection practices.
Integrating Recycling with Security
Once devices are destroyed, responsible disposal becomes the next priority. Electronics contain materials that should not end up in landfills.
Combining destruction with secure electronics recycling allows businesses to:
- Protect sensitive data
- Reduce environmental impact
- Support responsible waste management practices
This approach aligns with both security goals and sustainability efforts.
Common Mistakes to Avoid
Even well-intentioned businesses can make mistakes when handling employee devices. Being aware of common pitfalls can help you avoid unnecessary risks.
Delaying the Process
Waiting too long to collect or process devices increases the chance of loss or misuse. A clear timeline ensures that action is taken promptly.
Relying on Basic Deletion
Deleting files or performing a factory reset is not enough. Data can often be recovered unless it is properly destroyed.
Lack of Documentation
Without records, it becomes difficult to prove that devices were handled securely. This can create problems during audits or compliance checks.
Inconsistent Procedures
Handling each case differently leads to confusion and errors. A standardized process ensures reliability and accountability.
Training Your Team for Better Security
A data destruction plan is only effective if your team understands it. Training employees and managers on proper procedures helps reinforce security at every level.
Key areas to cover include:
- The importance of data protection
- Steps in the offboarding process
- Proper handling of company devices
- Reporting lost or missing equipment
When everyone is aware of their role, the risk of oversight decreases significantly.
The Value of Partnering with Professionals
Managing data destruction internally can be challenging, especially for businesses with frequent employee turnover. Professional providers bring expertise, equipment, and structured processes that reduce risk.
Working with a trusted partner offers:
- Consistent and secure handling of devices
- Access to specialized destruction methods
- Documentation for compliance and records
- Efficient processing of large volumes of equipment
This allows your team to focus on core business operations while ensuring data remains protected.
Creating a Culture of Data Responsibility
Beyond processes and tools, long-term security depends on building a culture where data protection is a priority.
Encourage practices such as:
- Treating company data as a valuable asset
- Following established security protocols
- Reporting concerns without delay
When data responsibility becomes part of everyday operations, the chances of accidental exposure are greatly reduced.
Moving Forward with Confidence
Employee turnover does not have to be a risk to your business. With a clear and structured data destruction plan, you can protect sensitive information, stay compliant, and maintain trust with clients and partners.
Taking proactive steps today helps prevent problems tomorrow. By integrating secure handling, professional destruction, and responsible recycling, your business can manage transitions smoothly without compromising data security.
If you are looking to improve device handling and data protection, Data Shredder Corporation provides reliable solutions such as a locked shredding collection bin to support your business needs. Learn more about creating a secure plan and protecting your information by visiting https://www.datashredder.net/.








Share On: