How Certified Data Destruction Builds Trust During High-Security Projects and Audits
How Certified Data Destruction Builds Trust During High-Security Projects and Audits
Why Verified Data Destruction Is Critical for Security, Compliance, and Client Confidence During Sensitive Projects
High security projects leave little room for uncertainty.
Whether your organization is preparing for a regulatory audit, completing a government contract, closing a sensitive facility, or upgrading critical infrastructure, every detail matters. Data protection is often at the top of that list. One overlooked hard drive or misplaced server can create questions that no company wants to answer.
That is why many businesses rely on certified data destruction partners rather than attempting to manage disposal internally. When handled properly, professional destruction services do more than eliminate data. They build confidence with auditors, clients, and stakeholders.
For companies working with Data Shredder Corporation, secure data destruction is not just a routine service. It is a way to demonstrate accountability when it matters most.
What Secure Data Destruction Involves
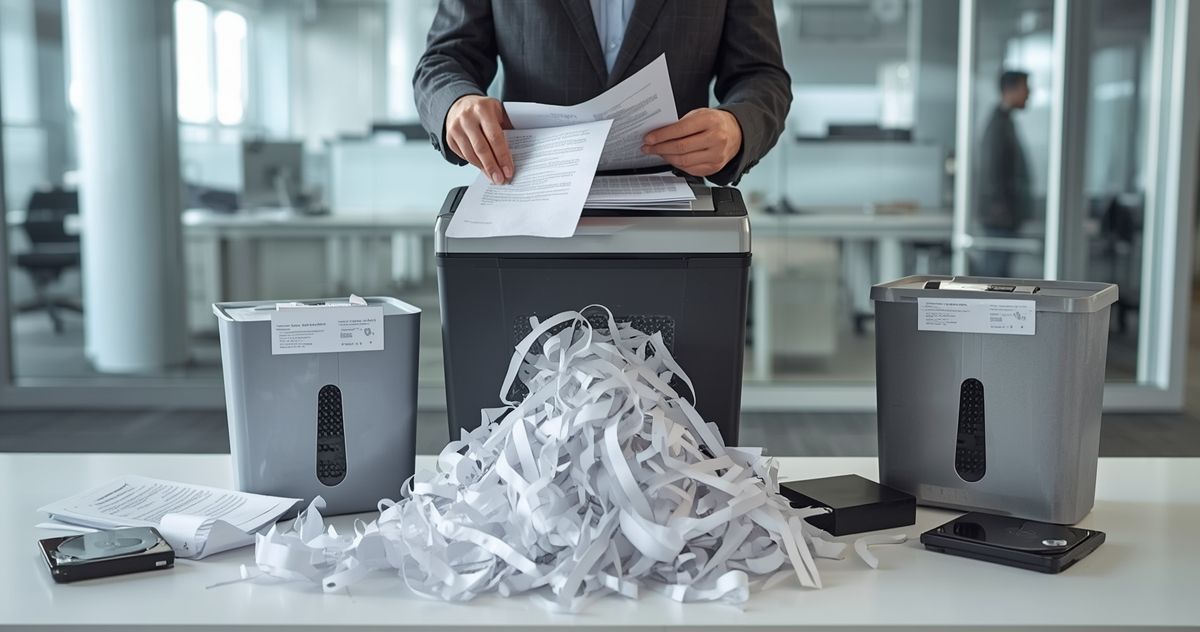
Secure data destruction ensures that data bearing devices are permanently destroyed so information cannot be recovered or reconstructed.
Organizations often accumulate a wide range of retired equipment, including:
- Hard drives
- Solid state drives
- Backup tapes
- Servers and storage arrays
- Laptops and desktop computers
When these devices reach the end of their lifecycle, they must be destroyed using approved methods. Professional providers use industrial grade shredding and specialized equipment designed specifically for electronic media.
Devices are securely transported and processed at controlled destruction facilities where strict procedures are followed. After the destruction process is complete, a Certificate of Destruction is issued. This documentation verifies that devices were destroyed according to recognized security standards.
Why Audits Require Clear Evidence
Auditors rarely rely on policies alone. They look for documented proof. In industries such as healthcare, finance, government contracting, and education, organizations must show that sensitive data has been disposed of securely. Many standards reference guidance such as the National Institute of Standards and Technology publication NIST Special Publication 800-88 for proper media sanitization.
During an audit, organizations may be asked to provide documentation that shows:
- What devices were destroyed
- When the destruction occurred
- What method was used
- Which certified provider performed the service
Professional destruction services simplify this process by providing detailed documentation that supports compliance records. When auditors can easily verify destruction records, the audit process tends to move more smoothly and efficiently.
Why Chain of Custody Matters
One of the most important aspects of secure data destruction is maintaining a documented chain of custody. Sensitive devices must be handled with strict security procedures from the moment they are collected until the moment they are destroyed. A reputable destruction provider follows carefully controlled processes that include:
- Secure collection procedures
- Locked transportation containers
- Controlled facility access
- Monitored destruction processes
- Detailed tracking and documentation
This structured approach ensures that data bearing devices are accounted for at every stage. For organizations managing confidential client information, proprietary research, or regulated data, clear chain of custody documentation helps reduce risk and demonstrate responsible data handling.
Building Client Confidence Through Verified Processes
Trust is not built through promises. It is built through consistent and verifiable processes. Imagine a company completing a contract that involves customer financial records. At the end of the project, the organization must confirm that all related storage devices have been permanently destroyed.
When destruction is handled by a certified provider with documented procedures, clients gain reassurance that their information has been eliminated properly.
Certificates of Destruction and detailed reporting provide the transparency needed to confirm that security requirements were met.
This level of accountability strengthens relationships and shows that your organization treats data protection seriously.
Supporting Government and Defense Related Projects
Government and defense contracts often require enhanced security procedures. These projects frequently involve strict guidelines regarding how sensitive information must be handled and destroyed. Contracts may specify approved destruction methods as well as documentation requirements.
Professional data destruction providers help organizations meet these expectations by offering:
- Secure handling of sensitive media
- Industrial grade destruction equipment
- Detailed documentation for compliance
- Processes aligned with recognized standards
By relying on certified destruction services, organizations demonstrate that they are following proper procedures and protecting sensitive information throughout the lifecycle of the project.
Managing Risk During Office Closures or Mergers
High security situations are not limited to audits or government work. Corporate transitions can also create sensitive moments.
Office closures, relocations, and mergers often involve equipment such as:
- Decommissioned servers
- Archived backup drives
- Retired laptops
- Legacy storage systems
These devices may contain years of internal records and confidential client information.
During times of organizational change, teams are often focused on logistics and operations. Secure destruction services provide a reliable solution by ensuring that outdated devices are handled properly and permanently destroyed.
Removing this responsibility from internal teams helps reduce the risk of overlooked assets.
Meeting Tight Project Deadlines
Audits and project timelines often require fast confirmation that data has been properly destroyed.
Waiting too long to address device disposal can slow down project completion or create unnecessary complications during final reviews.
Professional destruction services help streamline the process by providing efficient scheduling, secure transportation, and prompt documentation after destruction is completed.
This allows project managers and compliance teams to move forward with confidence.
Strengthening Internal Security Culture
Secure data destruction does not only support external compliance. It also reinforces internal security standards.
When organizations implement clear procedures for disposing of retired equipment, employees develop a stronger understanding of information security responsibilities.
Instead of allowing outdated devices to sit in storage closets or unused offices, organizations follow a structured process for proper destruction.
Over time, this reinforces a culture where data protection is treated as a continuous responsibility rather than an occasional task.
Supporting Responsible Electronics Recycling
Secure destruction and environmental responsibility can go hand in hand.
After data bearing components are destroyed, remaining electronic materials can be processed through responsible recycling channels. Metals, plastics, and other components are recovered and reused rather than sent to landfills.
Organizations seeking secure electronics recycling benefit from a process that protects sensitive information while also supporting sustainability goals.
Environmental responsibility is increasingly important to both clients and regulators, making proper disposal practices even more valuable.
What to Look for in a Data Destruction Partner
Not all providers offer the same level of security and documentation.
When selecting a partner, consider whether they:
- Follow recognized data destruction standards
- Provide detailed Certificates of Destruction
- Maintain secure chain of custody procedures
- Use industrial grade destruction equipment
- Offer clear communication throughout the process
A professional provider will guide your organization through the process and ensure that your documentation supports compliance requirements. Clear procedures and consistent reporting help maintain trust with both auditors and clients.
Turning Compliance into a Competitive Advantage
High security projects and regulatory audits can be demanding, but they also offer an opportunity to demonstrate strong operational standards.
Secure data destruction turns equipment disposal into a documented process that protects both your organization and your clients. It satisfies auditors, reduces risk, and reinforces your commitment to responsible data handling.
Instead of treating device disposal as an afterthought, incorporating professional secure e-waste destruction services into your security practices strengthens your credibility in industries where trust matters most.
If your organization is preparing for an audit, completing a sensitive project, or managing the retirement of data-bearing devices, visit https://www.datashredder.net/ to learn how Data Shredder Corporation can help you protect critical information with a
secure document console and fully documented data destruction services.








Share On: