From Microscopes to Monitors: Safely Disposing of Equipment That Still Contains Data
From Microscopes to Monitors: Safely Disposing of Equipment That Still Contains Data
Balancing Compliance, Security, and Sustainability in Equipment Decommissioning
When people think about data security, they often picture laptops, servers, and smartphones. While these devices certainly hold valuable information, they are not the only ones that pose a risk. Many types of equipment, including medical tools, lab devices, and office systems, can store sensitive data without it being obvious.
From microscopes used in research labs to monitors in everyday workspaces, modern equipment often includes internal storage or connected systems that retain information. If these items are not handled properly at the end of their lifecycle, they can become unexpected sources of data exposure.
Understanding how to safely dispose of such equipment is an important step in protecting your business, your clients, and your reputation.
The Hidden Data Inside Everyday Equipment
Technology has evolved quickly, and many devices now include digital components that were not present in older models. Even equipment that seems purely mechanical may contain embedded systems that store data.
Examples of equipment that may hold sensitive information include:
- Digital microscopes used in laboratories
- Medical imaging devices and diagnostic tools
- Office printers and multifunction copiers
- Security systems and surveillance equipment
- Point-of-sale systems and retail terminals
- Monitors with built-in storage or connectivity features
These devices may store anything from patient records and research data to login credentials and internal communications.
Because the data is not always visible, it is easy to overlook these risks during disposal.
Why Standard Disposal Is Not Enough
Many businesses assume that once equipment is no longer in use, it can simply be recycled or discarded. Unfortunately, this approach can leave data intact and accessible.
Basic steps like deleting files or resetting a device often do not fully remove stored information. In many cases, data can still be recovered using specialized tools.
Improper disposal can lead to:
- Data breaches and unauthorized access
- Compliance violations and potential fines
- Loss of customer or client trust
- Damage to business reputation
This is why a more secure and structured approach is necessary.
Identifying Devices That Require Special Handling
Before disposing of equipment, it is important to determine whether it contains any form of data storage.
Start by asking a few key questions:
- Does the device have internal memory or storage?
- Has it been connected to a network or system?
- Does it process, display, or transmit sensitive information?
If the answer to any of these is yes, the device should be treated as a data-bearing asset.
Creating a checklist for different types of equipment can help ensure nothing is missed during the disposal process.
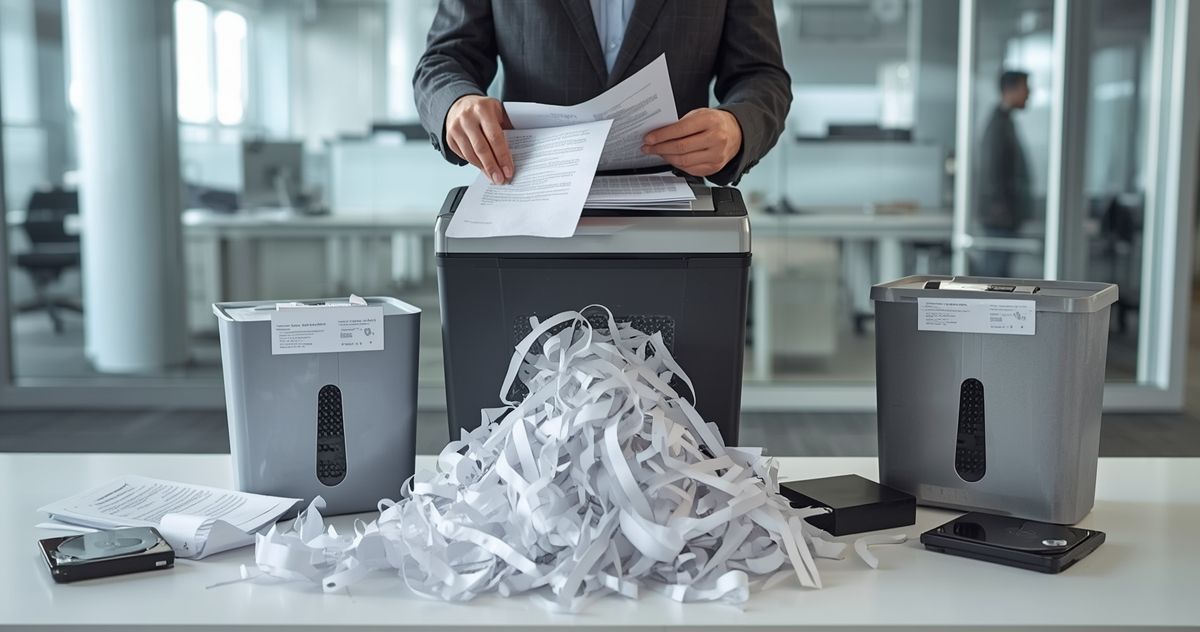
The Importance of Secure Data Destruction
Once a device is identified as containing data, the next step is ensuring that the information is permanently destroyed.
Professional data destruction services are designed to handle this process securely and efficiently. They go beyond basic deletion to ensure that data cannot be recovered under any circumstances.
For devices with internal drives or storage components, hard drive shredding is one of the most effective methods. This process physically destroys the storage media, making it impossible to access the data again.
Using certified hard drive destruction also provides documented proof that the process was completed according to strict standards.
Handling Specialized Equipment
Some equipment requires extra care due to its complexity or the sensitivity of the data it contains.
Medical and Laboratory Devices
Devices used in healthcare and research often store highly sensitive information, including patient data and study results. These items must be handled in accordance with strict regulations.
Proper destruction ensures that confidential information remains protected even after the equipment is retired.
Office Equipment
Printers, copiers, and fax machines are often overlooked, yet they frequently store copies of documents on internal drives. These devices should be included in any secure disposal plan.
Security Systems
Surveillance systems and access control devices may store video footage and entry logs. These records can be sensitive and should be destroyed securely.
Combining Security with Environmental Responsibility
Disposing of equipment is not just about protecting data. It is also about managing electronic waste in a responsible way.
Partnering with a provider that offers secure electronics recycling ensures that materials are handled properly after destruction. This helps reduce environmental impact while maintaining data security.
Responsible recycling practices include:
- Recovering reusable materials
- Preventing harmful substances from entering landfills
- Following environmental regulations
This approach supports both sustainability and compliance goals.
Creating a Clear Disposal Policy
To manage equipment safely, businesses should establish a clear and consistent disposal policy. This helps ensure that all departments follow the same procedures.
A strong policy should include:
- Guidelines for identifying data-bearing equipment
- Steps for secure collection and storage
- Approved methods for data destruction
- Documentation requirements for each item
Having a written policy reduces confusion and helps maintain accountability across the organization.
Training Teams to Recognize Risks
Employees play an important role in protecting data during equipment disposal. Without proper training, it is easy for items to be overlooked or handled incorrectly.
Training should focus on:
- Recognizing devices that may contain data
- Following established disposal procedures
- Reporting equipment that is no longer in use
- Understanding the importance of data security
When teams are informed and prepared, the risk of mistakes is greatly reduced.
The Benefits of Working with a Trusted Partner
Handling equipment disposal internally can be complex, especially for organizations with a wide range of devices. Partnering with professionals simplifies the process and ensures consistent results.
A reliable provider offers:
- Expertise in handling different types of equipment
- Secure and verified destruction methods
- Documentation for compliance and records
- Efficient processing of large volumes
By using data shredding services, businesses can ensure that all data-bearing equipment is handled with care from start to finish.
Looking Beyond the Obvious
Data security is not limited to computers and servers. As technology continues to evolve, more devices are capable of storing information in ways that are not always visible.
Taking a broader view of what constitutes a data risk is essential. By recognizing that even everyday equipment can hold sensitive information, businesses can take proactive steps to protect themselves.
A thoughtful approach to disposal helps prevent unexpected vulnerabilities and keeps data secure at every stage.
Safely disposing of equipment that still contains data is not just a technical task. It is a key part of responsible business operations. With the right processes in place and the support of experienced professionals, you can protect your information while managing equipment practically and sustainably.
If your business is ready to improve how it handles outdated or unused equipment, Data Shredder Corporation can help you take the next step with solutions like a secure document console. Our services are designed to protect your data and support responsible disposal practices. Learn more by visiting https://www.datashredder.net/.








Share On: